1,300%
Growth rate of DDoS attacks larger than 250 GBit/s
As ransomware attacks continue to make front page news, Distributed Denial of Service (DDoS) attacks may have appeared to decrease. In reality, threat actors continue to engage in DDoS attacks, especially with continued geopolitical tensions, but many go unreported making it difficult to quantify the risk and impact. In fact, over the past three years, DDoS attacks accounted for 28% of cyber threats, but organizations were only moderately effective at detecting and responding to them.
Further, research from March 2022, notes:
Growth rate of DDoS attacks larger than 250 GBit/s
was the most attacked industry in 2021 - target of over 25% of all attacks
of all DDoS attacks in 2021 were Network flood attacks
of all DDoS attacks in 2021 were Transmission Control Protocol (TCP) attacks
While the financial services industry is a major target for threat actors, all industries face DDoS risks. During January 2022, a number of DDoS attacks impacted organizations across the financial services, IT software, IT infrastructure, government and telecommunications industries.
With rising numbers of attackers and evolving methodologies, the attacks became more complex, shifting in frequency and increasing in intensity. By understanding how DDoS attacks work and how they can impact business operations, organizations can more effectively mitigate risk.
In a distributed denial of service (DDoS) attack, threat actors use multiple machines to send high volumes of requests to networks or servers, ultimately overwhelming them with too much traffic and causing them to become overwhelmed. The malicious actors control the set of infected devices, known as a botnet, and the overloaded network is unable to respond to legitimate requests causing a "denial of service."
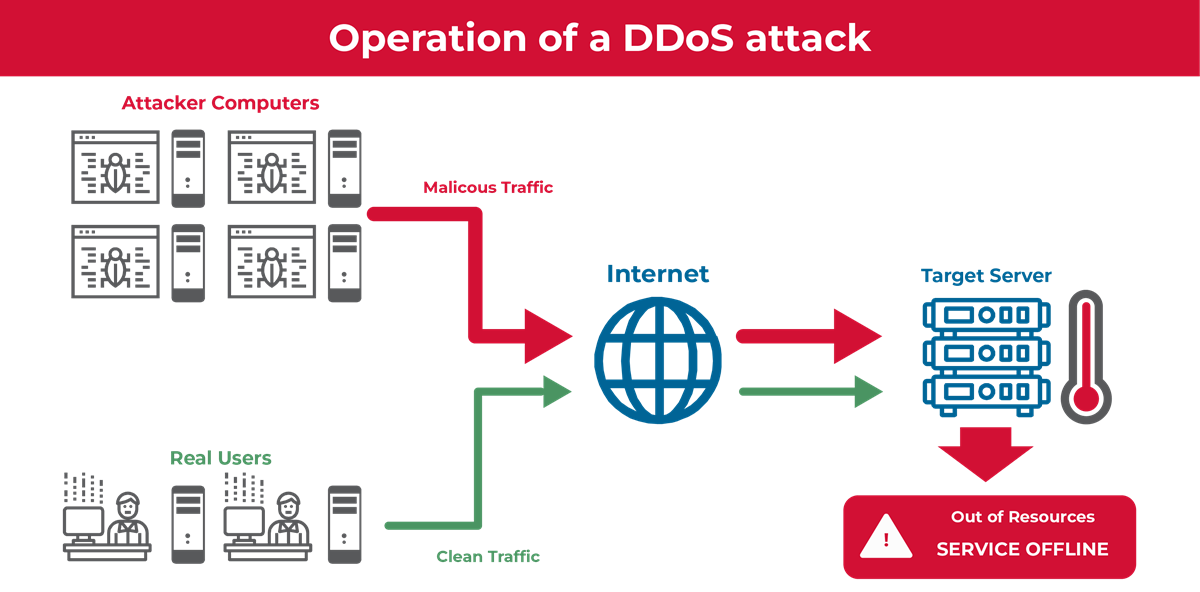
In the first step of a DDoS attack, the threat actors exploit a security vulnerability or device weakness in internet-connected devices. They then install malware on the device, usually a command and control software, that allows them to tell the devices what to do. The individual devices are called “zombies” or “bots,” and collectively they are known as botnets. Each device sends requests to the targeted network or server, ultimately overloading the resource and making it unable to respond to any requests.
As organizations adopt new technologies, threat actors also evolve their methodologies, including the ones used for DDoS attacks.
Some examples of the evolution of DDoS attacks include:
Since a DDoS attack disrupts networks and servers, they usually lead to business downtime and in turn, can cost companies hundreds of thousands of dollars, if not millions. This can include both internal or customer-facing resources and can lead to:
With more companies delivering digital customer experiences, a DDoS attack can prevent customers from accessing applications and data. For example, a DDoS attack against a Voice-over-Internet-Protocol (VoIP) company last autumn led to service disruption, preventing customers from sending or receiving calls. When reliability and security become a concern, customers will take their business elsewhere.
Companies in the business-to-business space need to consider whether service downtime will lead to a contract violation. In this case, the organization may need to pay a penalty, or the customer may choose to terminate the contract. Companies must have a solution in place to mitigate these types of attacks.
Business applications and organizational networks can also be impacted by a DDoS attack. This means that employees will be unable to access the resources they need to do their jobs, reducing productivity and impacting profits.
Just like any other attack type, organizations need to respond to a DDoS attack promptly. They need to contain the malware and restore all devices, systems, and networks to their pre-attack state.
When DDoS attacks are used to mask data exfiltration, companies may find that the initial outage also leads to privacy violations and potential lawsuits. Not only are these increased costs, but they can take a long time to resolve.
DDoS attacks often begin with subtle changes in network traffic or resemble maintenance issues.
When trying to determine whether an organization has experienced a DDoS attack, security teams usually look for some of the following indicators:
Network and device security are fundamental to preventing a DDoS attack. Organizations need anti-virus solutions to help protect all devices, including routers, from malware that turns devices into bots. Additionally, strong passwords for routers and internet-connected devices provide a layer of security preventing threat actors from leveraging these devices as part of their botnets.
SoftwareOne’s portfolio of managed security services enables customers to create proactive security programs. Our vulnerability assessment and penetration testing services give you a way to find any security weaknesses or vulnerabilities that threat actors can use as the first step in a DDoS attack. With our Managed Detection and Response (MDR) services, customers gain more robust incident detection capabilities for faster investigation and response. Finally, with our incident response and security testing, you’re able to create a cyber-resilient program that incorporates containment and recovery to get your customers and workforce members up-and-running faster.
Activate around-the-clock threat protection with SoftwareOne’s Managed Detection and Response. Protect your organization from the unknown.
Activate around-the-clock threat protection with SoftwareOne’s Managed Detection and Response. Protect your organization from the unknown.